Enhancement
This release gives customers a powerful new way to manage security at scale with the new Organization Dashboard - providing a unified view across all projects in one place. 🚀
In addition, key enhancements to STAR, scan and discovery management, project visibility, repeater controls, and dashboard capabilities deliver greater control, clearer insights, and more streamlined workflows. Helping teams work faster and make better decisions with less effort.
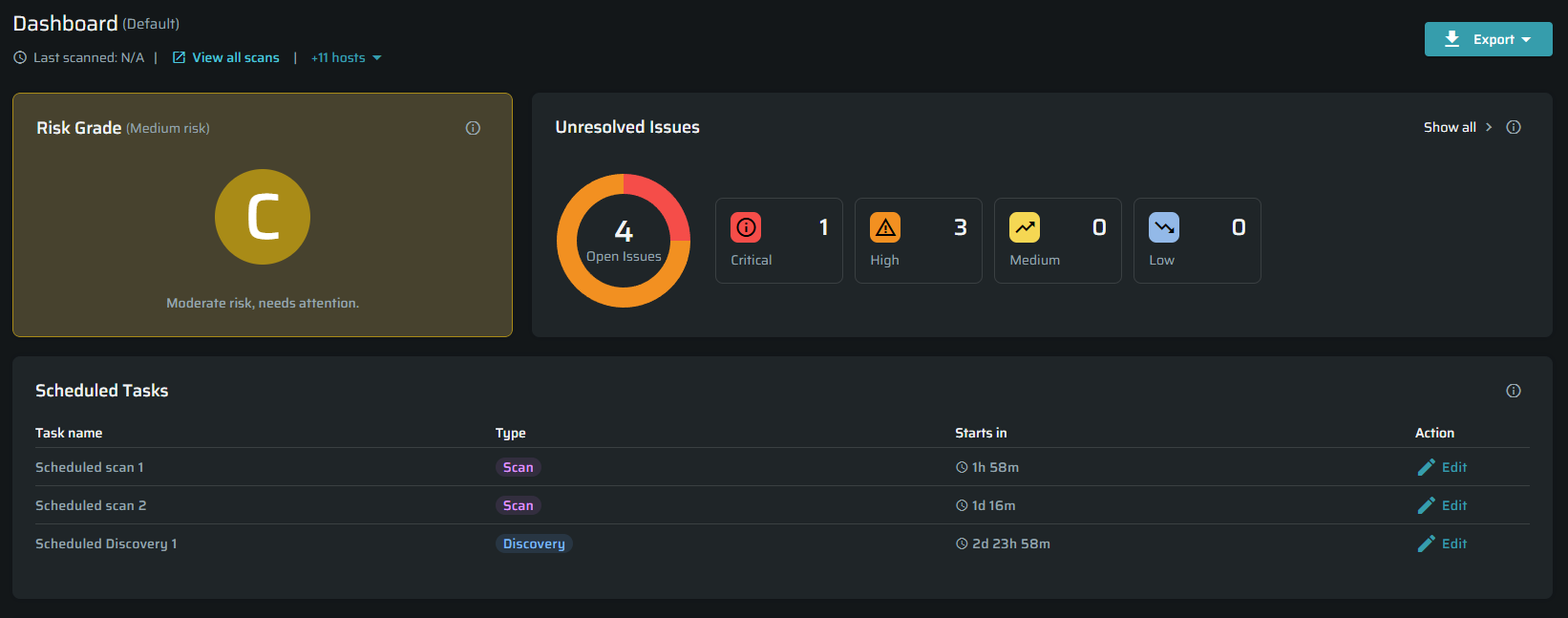
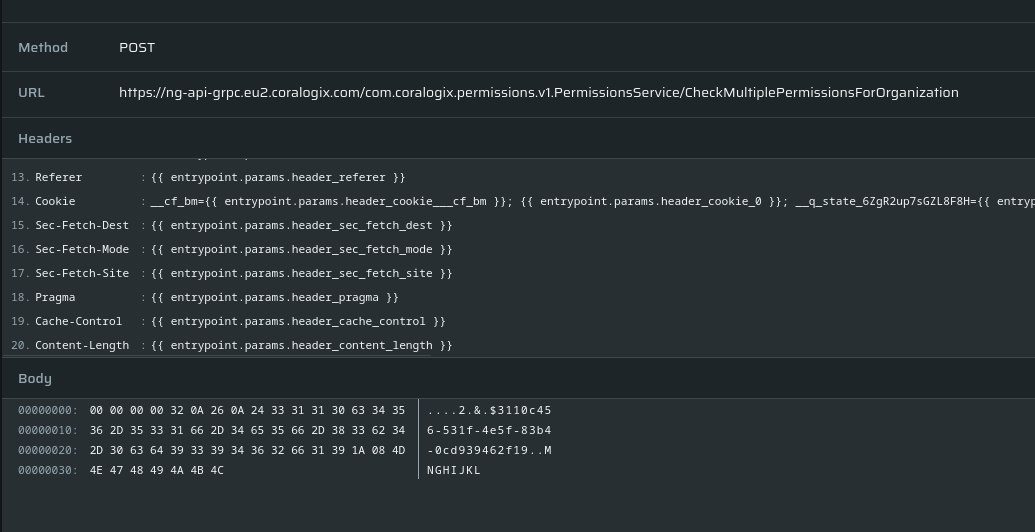
Organization Dashboard
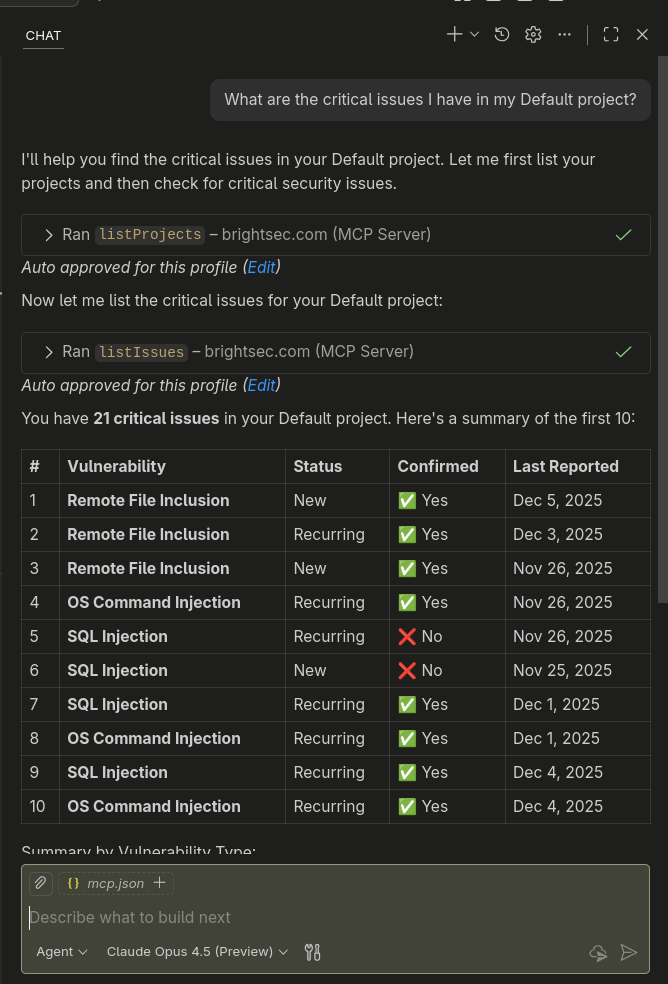
The new Organization Dashboard provides a centralized view of your security posture across all projects, allowing you to monitor risk, track progress, and prioritize actions from a single place.
It includes a set of widgets that provide quick insights into project activity, overall security grade, unresolved vulnerabilities, remediation trends, scan execution, entrypoint coverage, and aging issues - helping you quickly identify risks and make informed decisions.
For more information, visit the Organization Dashboard user guide
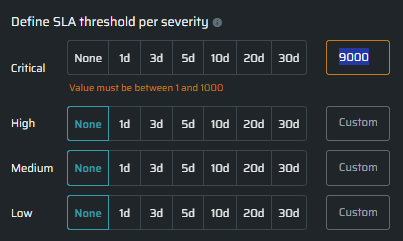
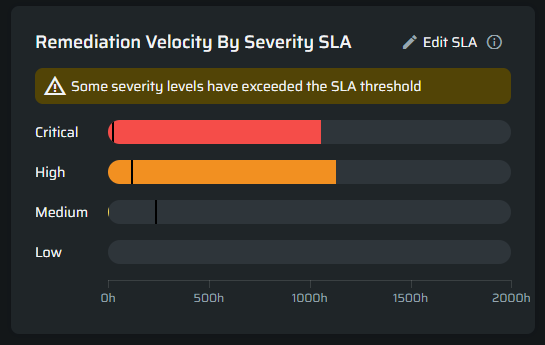
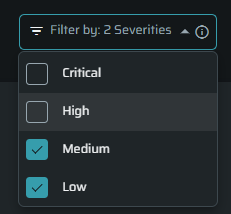
Filter Project Dashboard by Severity
A global Severity Filter has been added to the Project Dashboard, allowing users to focus on specific vulnerability severities such as Critical or High.
Relevant widgets update dynamically to reflect the selected severity, enabling more focused analysis and prioritization.
Affected Widgets
- Security Grade - calculated based only on the selected severity and reflects the highest risk within that scope
- Open vs Fixed Trend - shows trends only for the selected severity
- Top 10 Aging Issues - displays only issues matching the selected severity
- Remediation Velocity by Severity (SLA) - Showing only the selected severity bar
For more information, visit the Dashboard Severity Filter user guide
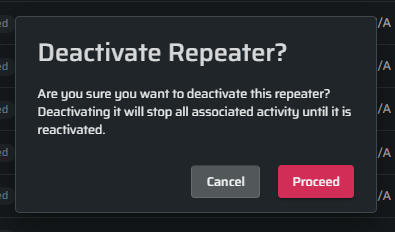
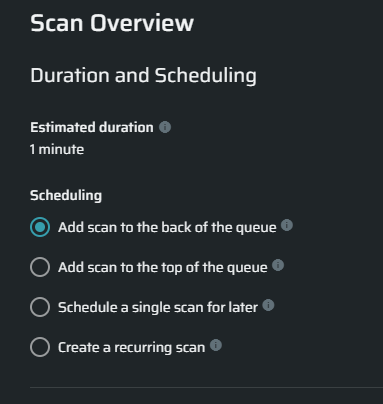
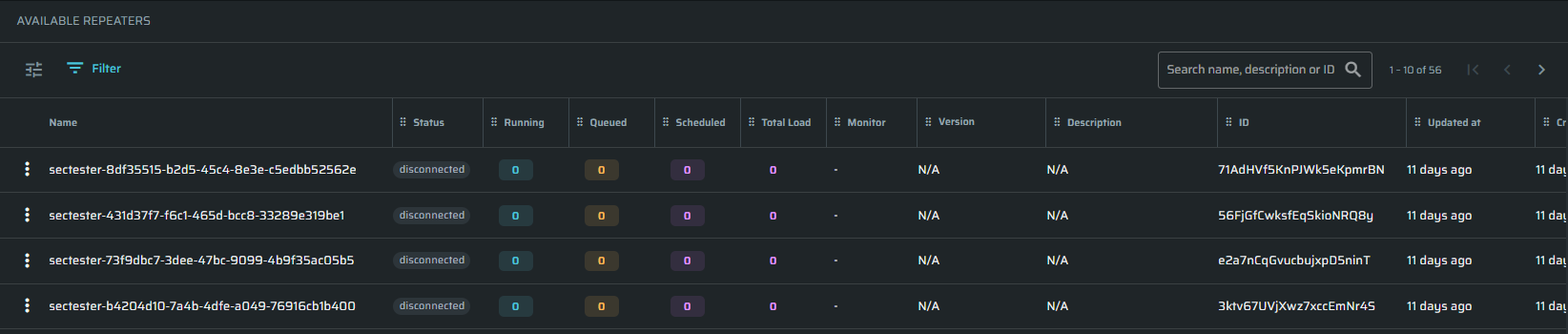
Runtime Indicators for Repeaters
Runtime workload indicators have been added to the Repeater settings pages, showing queued, running, and scheduled executions per repeater, along with connectivity status and contextual tooltips.
This enhancement helps users make better decisions when selecting repeaters, avoid overload, and balance workloads more effectively. If runtime data is unavailable, a fallback state is displayed.
V2 of this feature will extend these indicators to the repeater selection dropdown in Scan, Discovery, and Authentication flows.
For more information, visit the user guide for Repeater Runtime Indicators
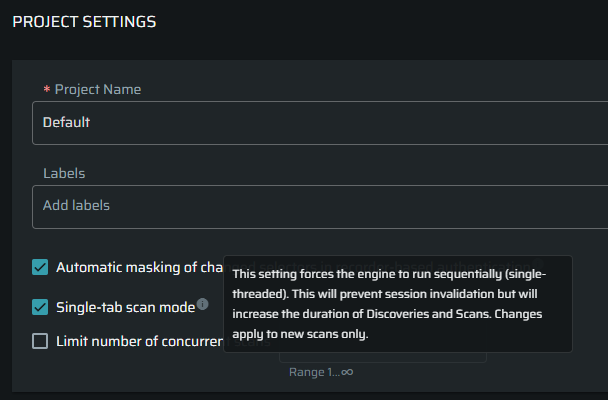
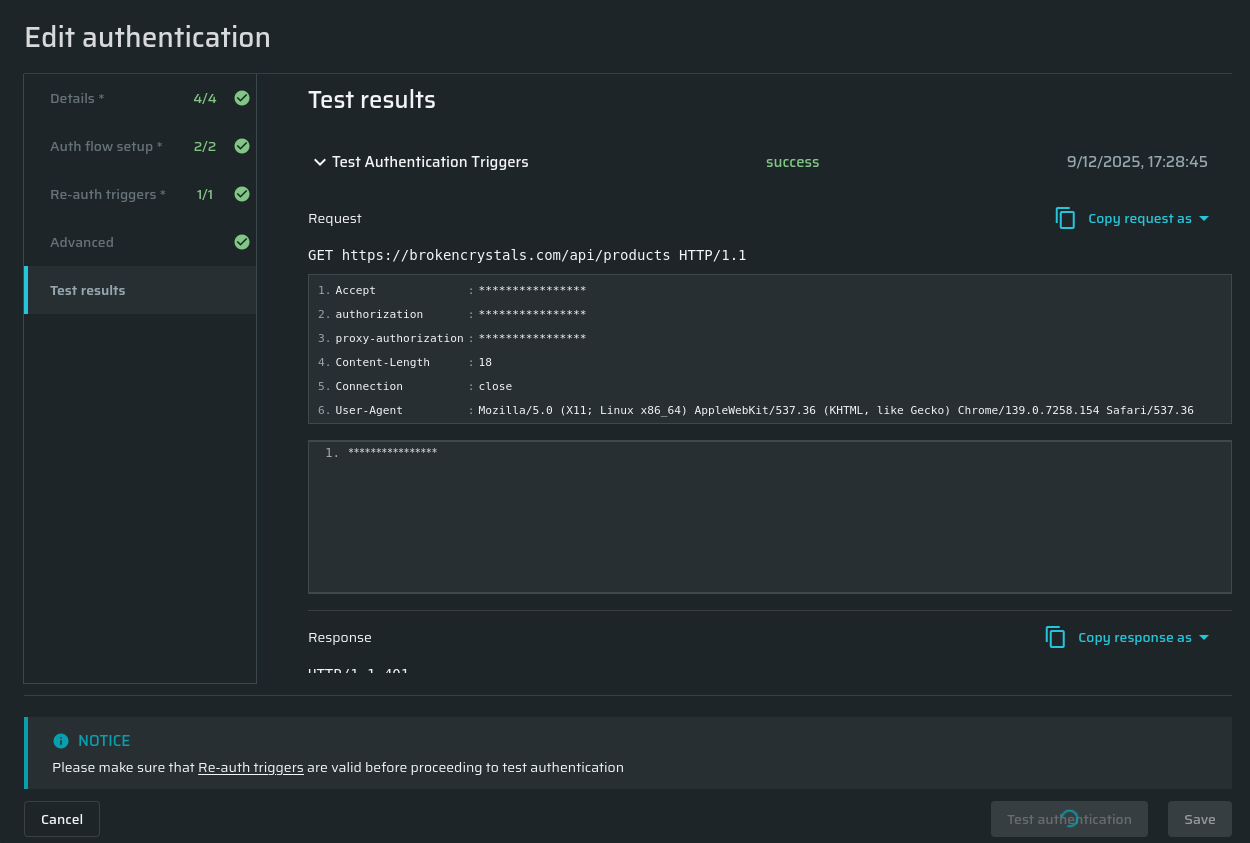
Limit Repeater Selection to One Per Scan
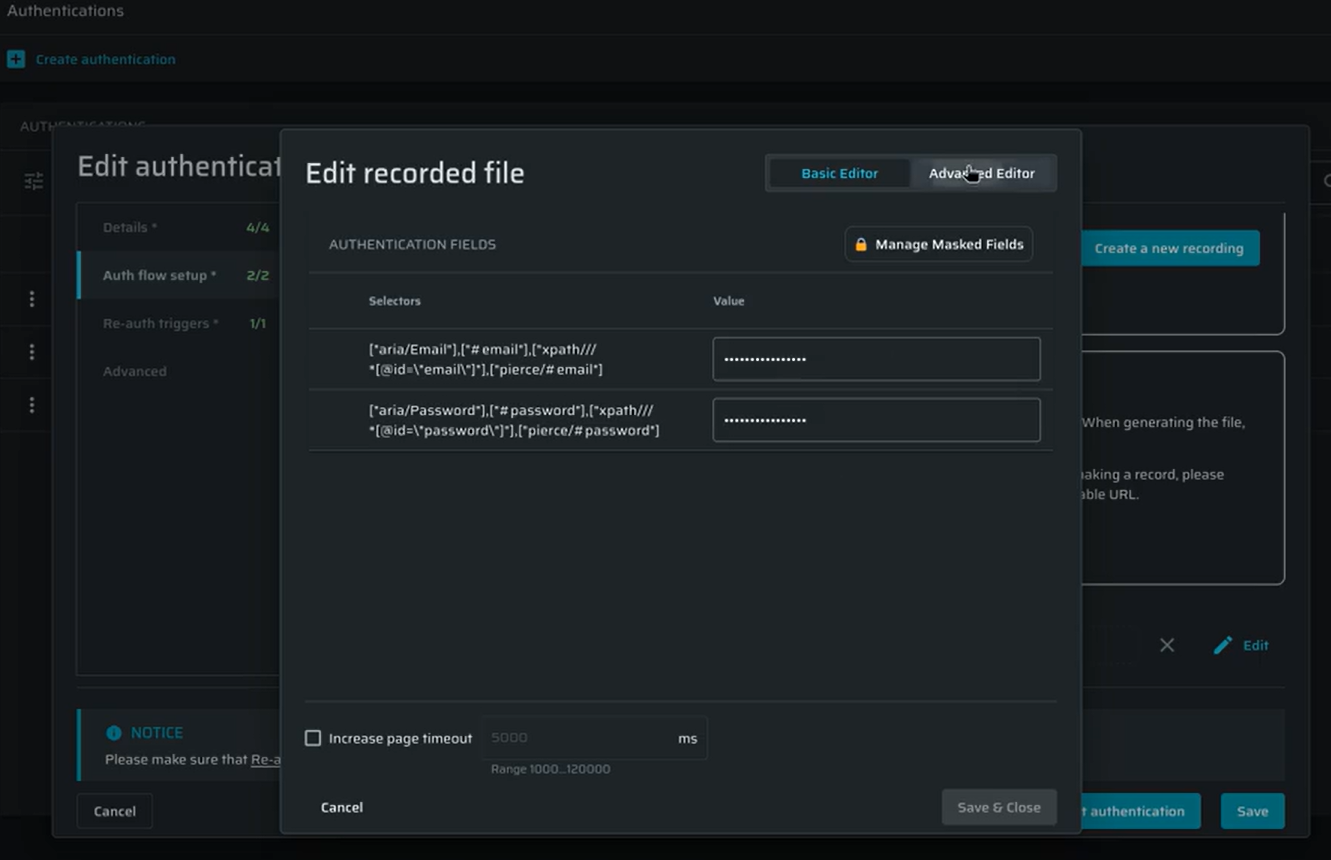
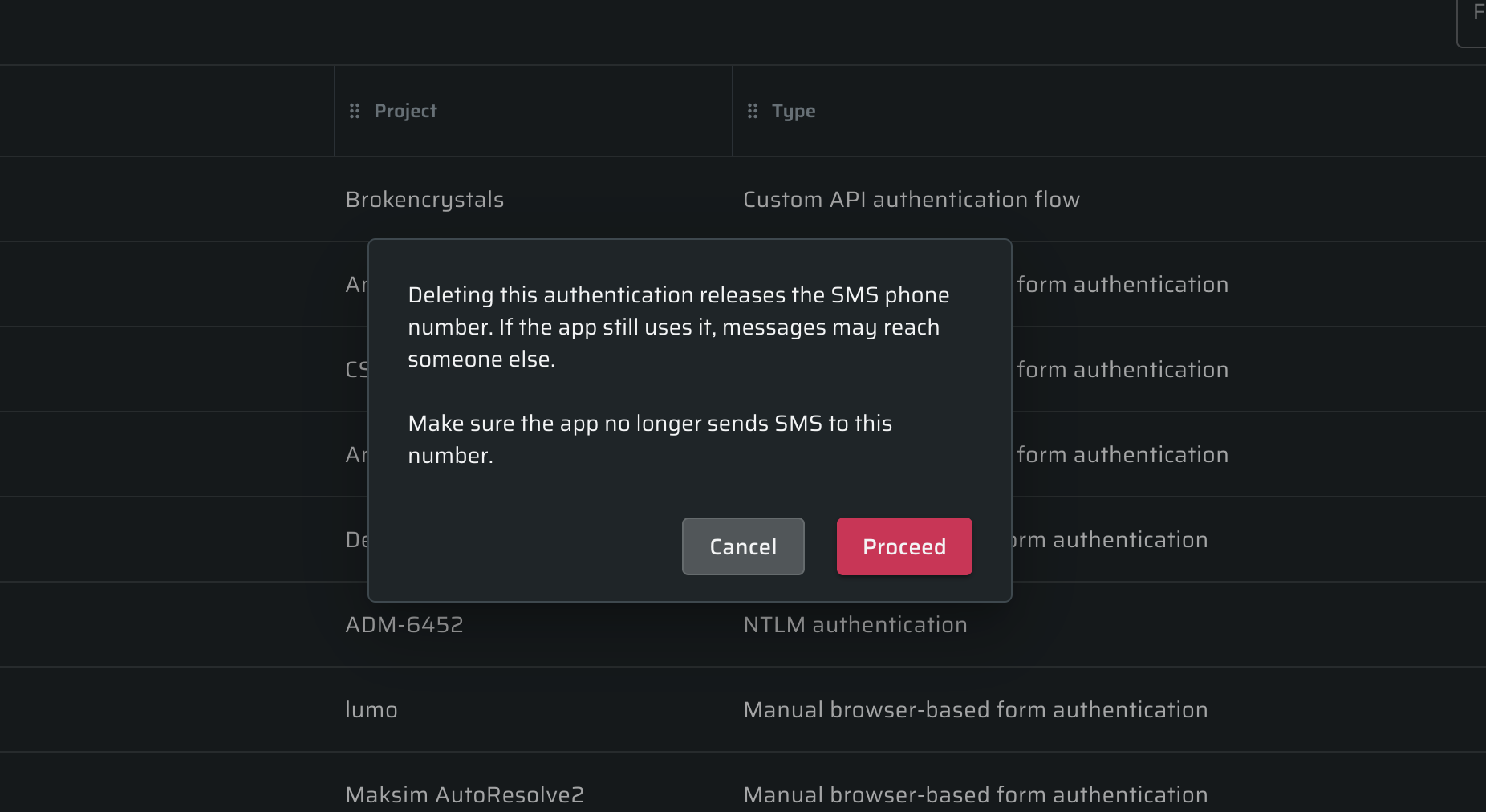
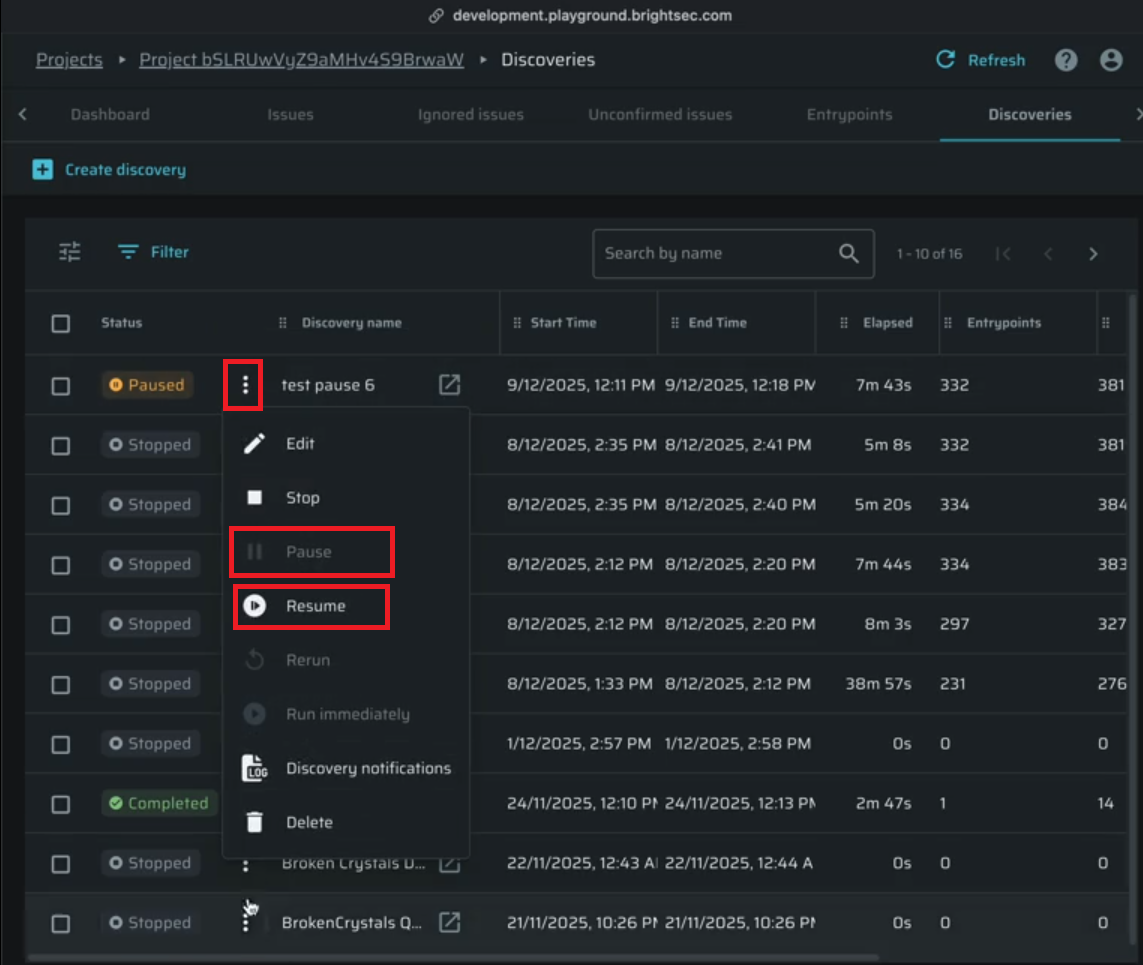
Repeater selection in Scan, Discovery, and Authentication configurations is now limited to a single repeater.
This aligns with current engine capabilities, as multiple repeaters are not supported per task. The update reduces confusion and ensures the UI and API accurately reflect system behavior.
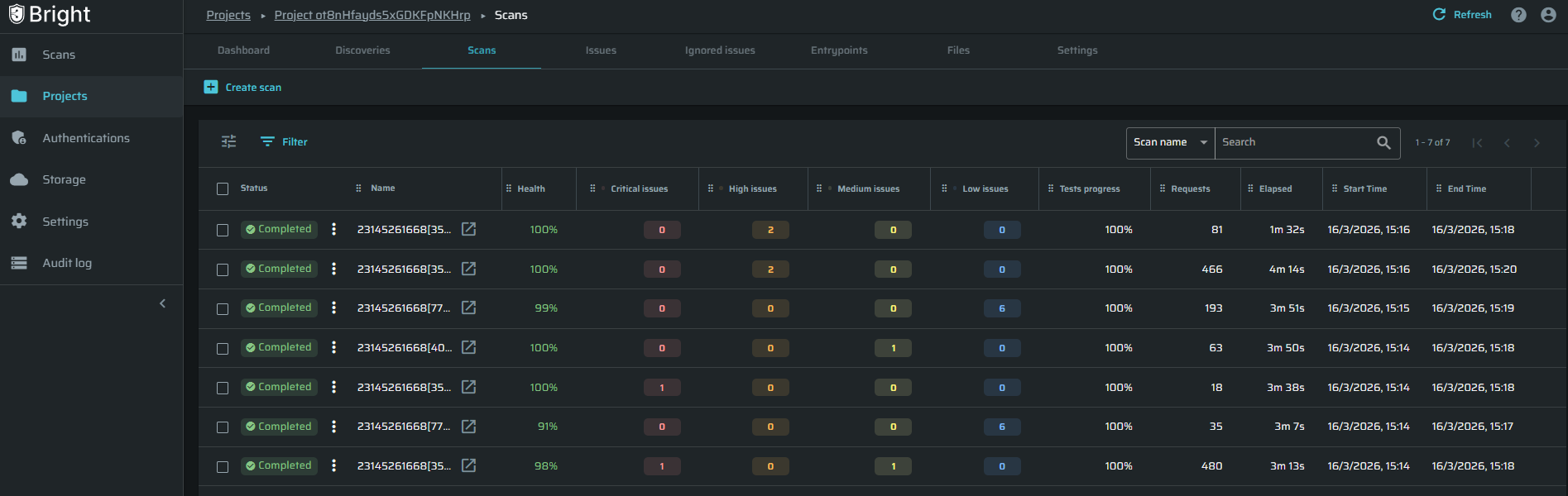
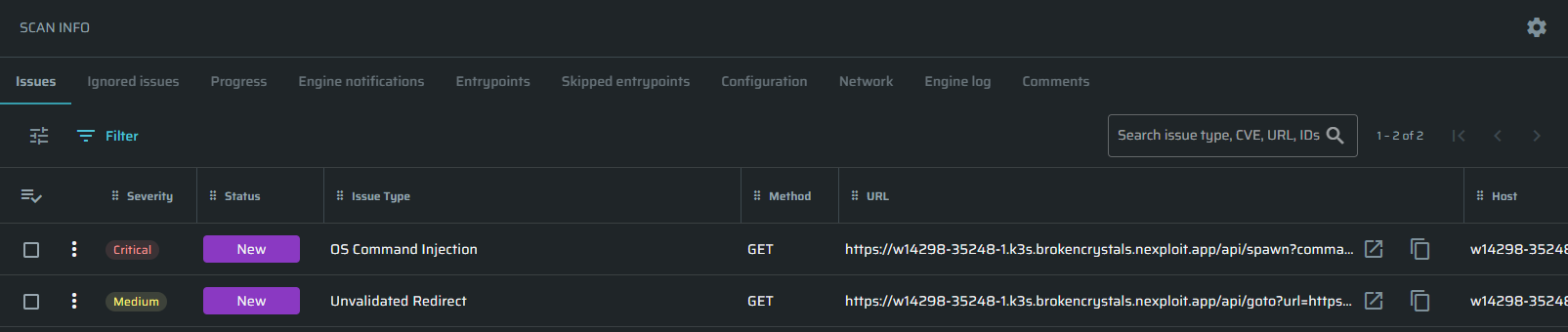
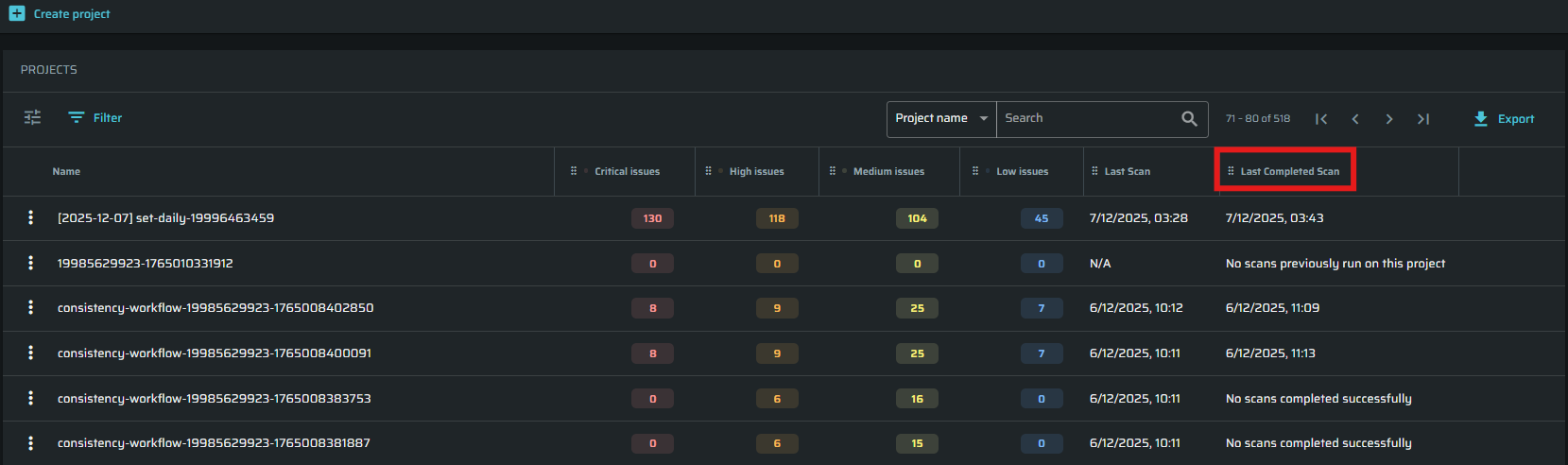
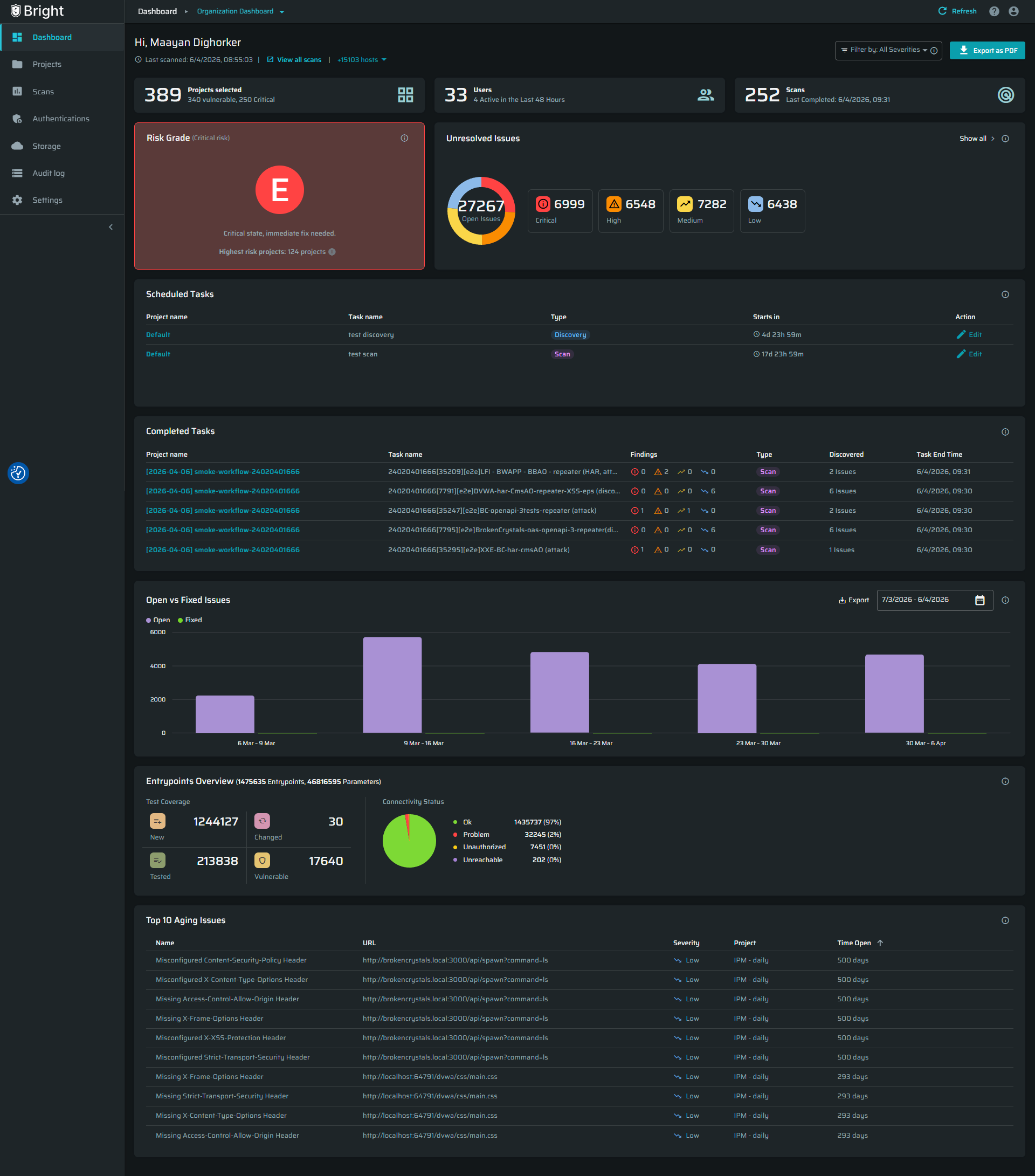
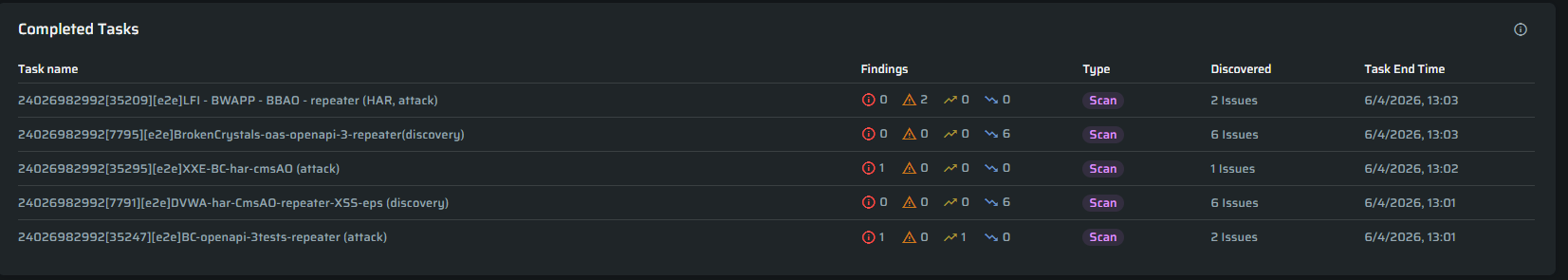
New Completed Tasks Widget
A new Completed Tasks widget has been added to the Project Dashboard.
It displays the most recently completed scans and discoveries, including scan name, type, severity breakdown, total issues or entrypoints, and completion time.
This provides quick access to recent results in one place and improves visibility into scanning activity.
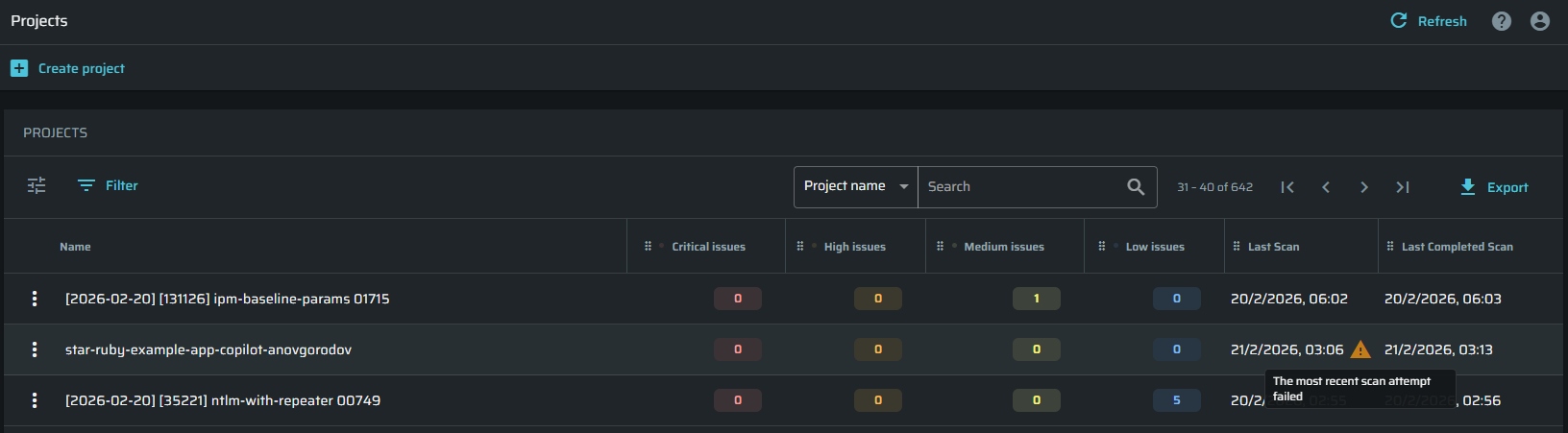
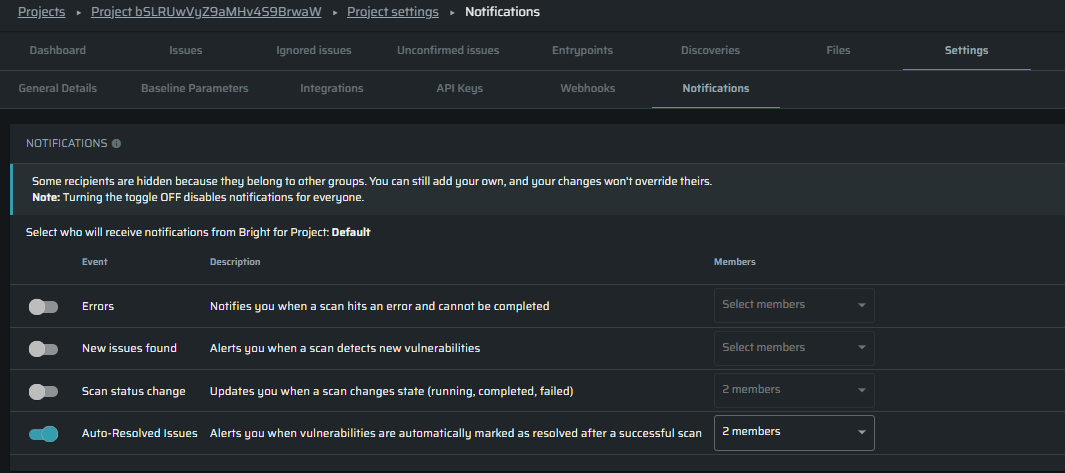
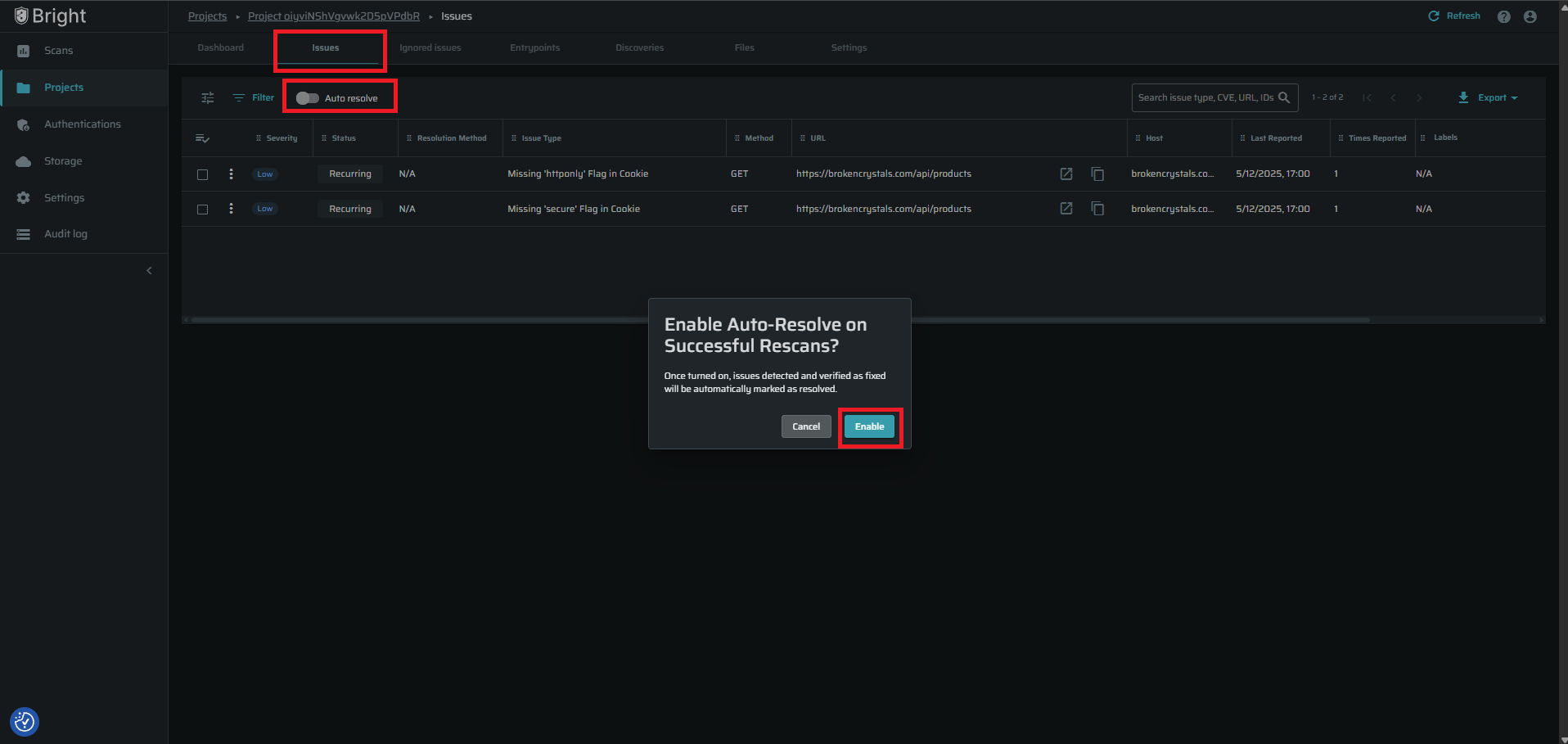
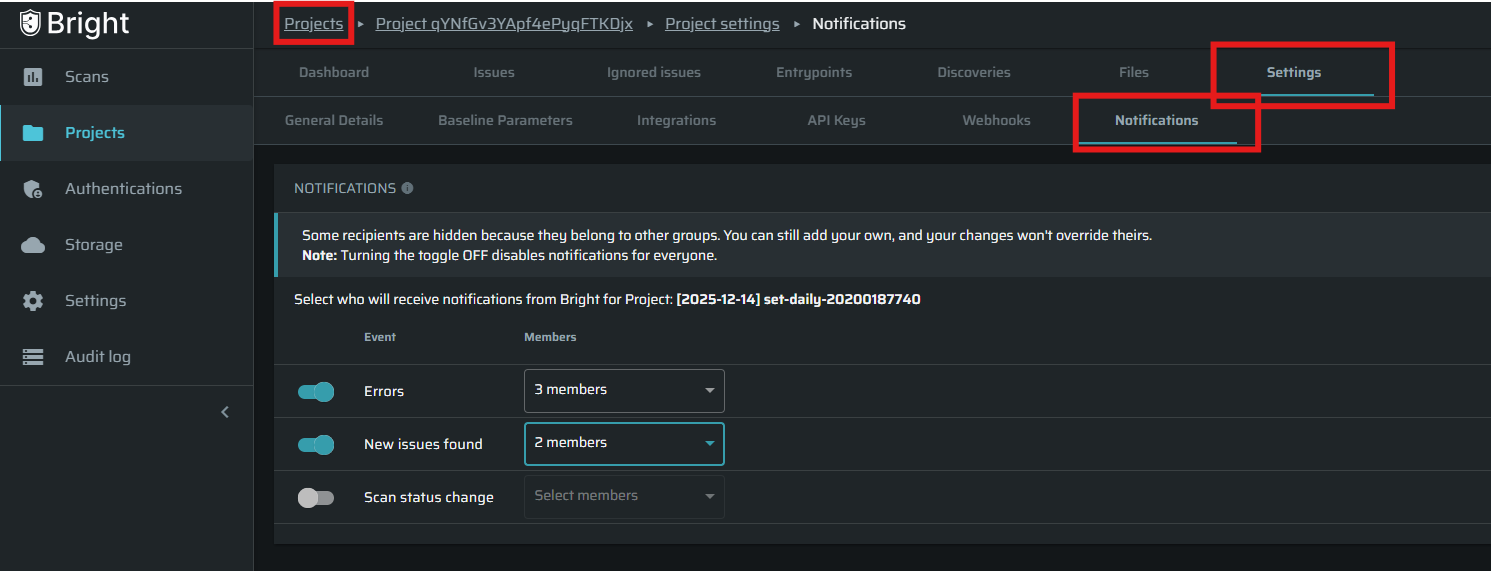
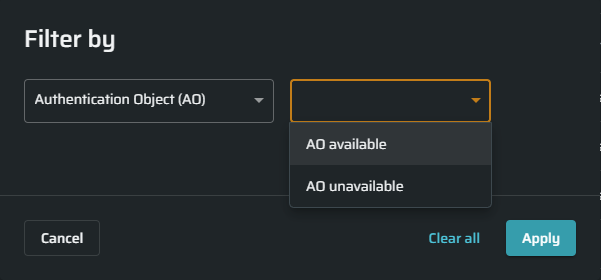
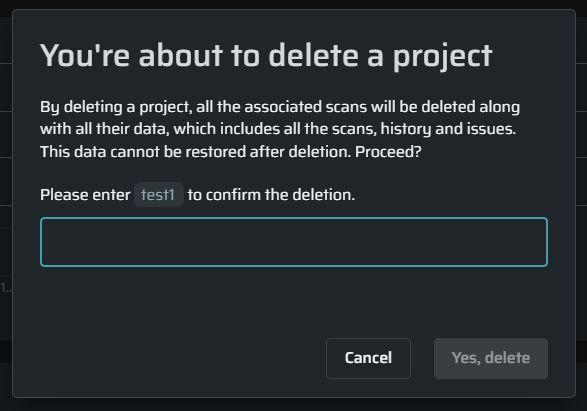
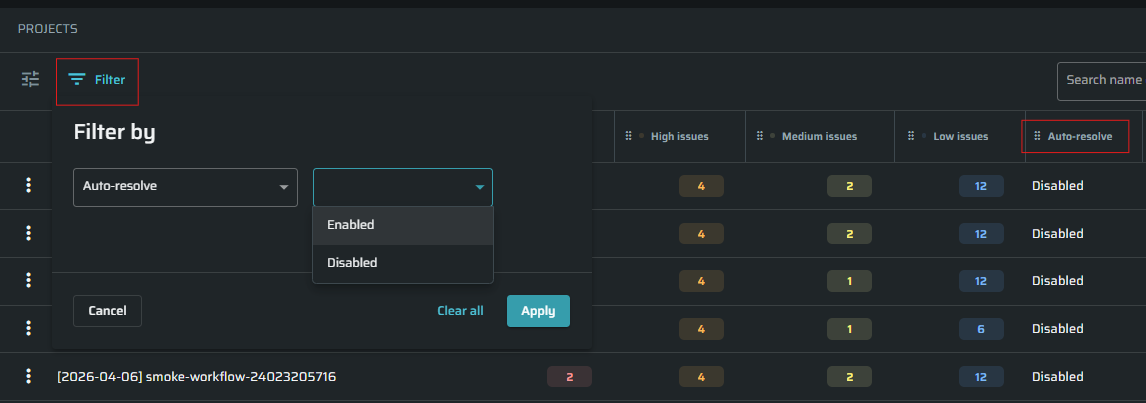
Filter Projects by Auto-Resolve Status
Users can now filter and sort projects based on their Auto-resolve status using a new column and filter options in project views.
This makes it easier to identify and manage projects with auto-resolve enabled or disabled, improving visibility and streamlining project selection.
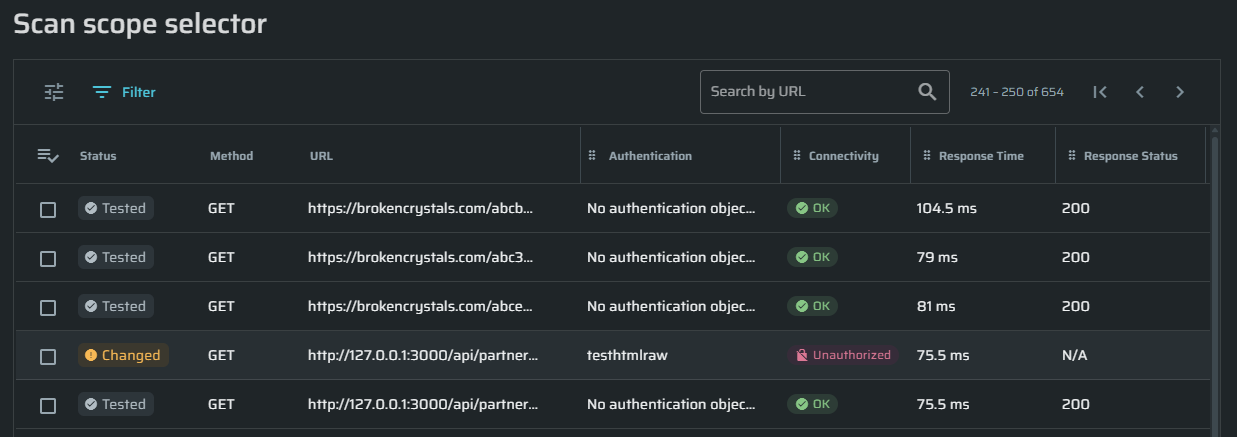
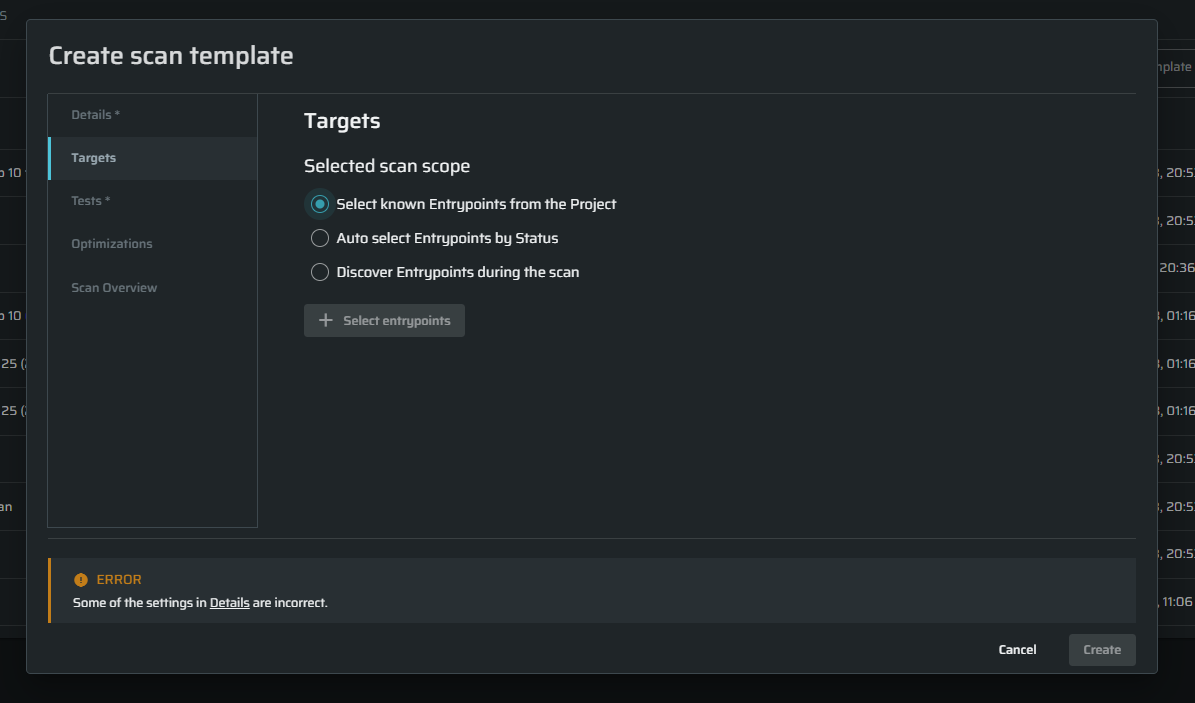
Align Template Targets with Scan Configuration
The Targets tab in the Scan Template creation flow has been aligned with the Scan Configuration page to ensure templates remain generic and reusable.
This improves consistency, reduces configuration errors, and keeps templates environment-agnostic.
Additionally:
- Repeater selection is now optional in templates
- If selected, the repeater is automatically applied during scan configuration
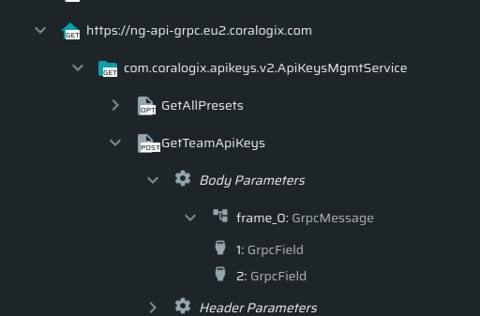
Enable API Keys to Access Dashboard Widgets
API keys with the appropriate scope can now retrieve Project and Organization dashboard widget data programmatically, matching what users see in the UI.
Access respects existing project-level permissions and uses the projects:read scope, ensuring secure and controlled data access. The API documentation has been updated accordingly.
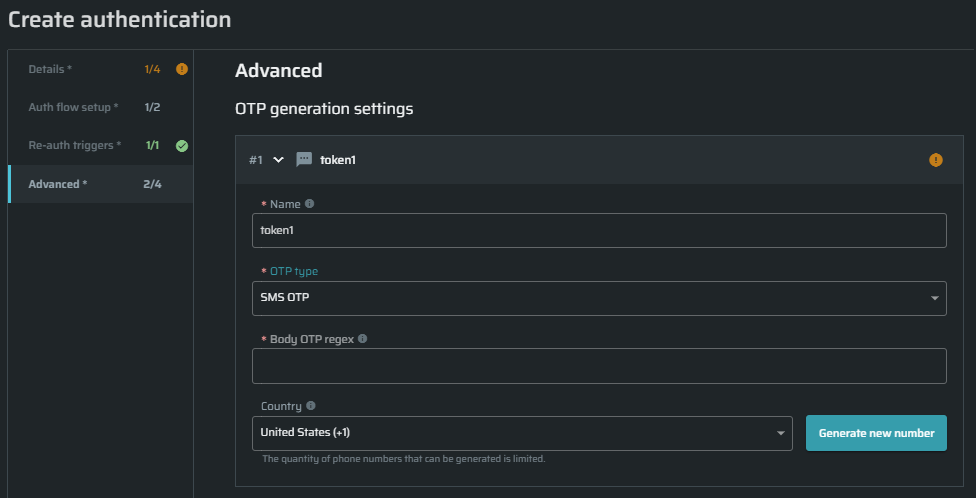
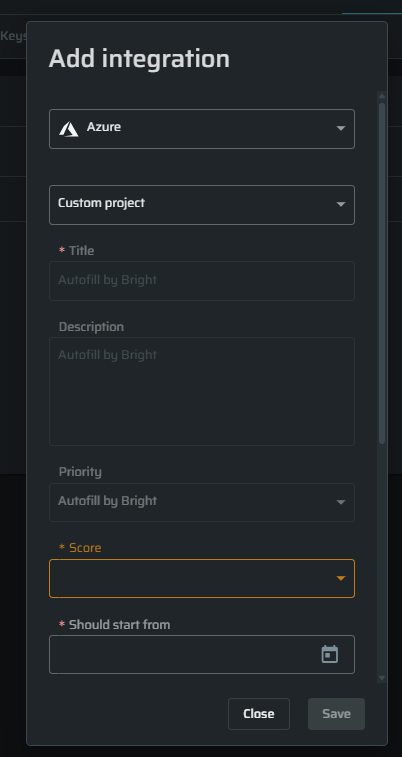
STAR Enhancements ⭐
STAR: BitBucket Support
STAR now supports working with Atlassian Bitbucket code repositories and BitBucket Pipelines CI/CD service.
Visit the user guide to see how to connect BitBucket code source
Changes Notice - Unconfirmed Issues
As part of our ongoing efforts to improve the accuracy and reliability of our security testing, we are updating how unconfirmed issues are handled in the platform.
Effective May 5th, the following changes will take place:
-
Unconfirmed Issues
New unconfirmed issues will no longer be generated.
Existing unconfirmed issues will remain in the system, but will not be automatically removed. -
MongoDB (NoSQL) Injection Test
This test will be deprecated and removed from the platform, as it primarily generated unconfirmed issues.
These changes are intended to reduce noise and help you focus on verified, actionable findings.
If you would like to fully remove existing unconfirmed issues from your environment, please contact our support team.
Important: These changes do not impact any API functionality or existing API calls.